What are the risks of DoS and DDoS attacks?

DoS attacks - these are attacks that lead to the paralysis of workserver or personal computer due to a huge number of requests, with a high rate of incoming to the attacked resource. If such an attack is carried out simultaneously from a large number of computers, then in this case one speaks of DDoS attack.
DoS - Denial of Service - an attack on the "denial of service". You can accomplish this attack in two ways. With the first method for a DoS attack, the vulnerability of the software installed on the attacking computer is exploited. With such a vulnerability on the computer, you can cause a certain critical error, which will lead to a malfunction of the system.
In the second method The attack is carried out by simultaneously sending a large number of packets of information to the attacked computer. According to the principles of data transfer between computers on the network, each packet of information sent by one computer to another is processed for some certain time.
If at the same time the computer receives moreone request, then the packet becomes a "queue" and takes up some amount of physical resources of the system. Therefore, if a large number of requests are simultaneously sent to the computer, an excessive load will cause the computer to "hang" or disconnect from the Internet. This is exactly what the DoS attack organizers need.
DDoS-attack is a kind of DoS-attack. Distributed Denial of Service - "distributed denial of service"is organized with the help of a very large number of computers, so that the attack can be affected by the server, even with very high bandwidth Internet channels.
Sometimes the effect of a DDoS attack "works" accidentally. This happens if, for example, a site on the server has been linked to a popular Internet resource. This causes a powerful spike in site traffic (splashdot effect), which acts on the server similar to the DDoS-attack.
DDoS-attacks, unlike simple DoS-attacks, more oftenall are spent for commercial benefit, after all for the organization of DDoS-attack hundreds of thousands of computers are needed, and such enormous material and time costs can not afford to everyone. To organize DDoS-attacks, cybercriminals use a special network of computers - botnet.
Botnet - a network of viruses infected with a special kind of computer-"zombie". Each such computer can be attacked by an attackermanage remotely, without the knowledge of the owner of the computer. With the help of a virus or a program artfully masked as "useful content," a malicious code is installed on the victim's computer, which is not recognized by the antivirus and works in "invisible mode." At the right time, on the command of the botnet owner, this program is activated and starts sending requests to the attacked server.
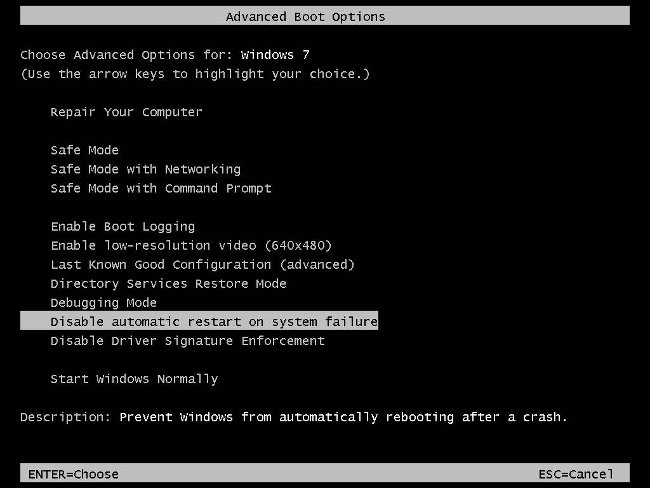
When conducting DDoS attacks, attackers often use "DDoS cluster" - a special three-level architecture of the computer network. Such a structure contains one or more control consoles, from which a signal is directly sent about the DDoS attack.
The signal is transmitted to main computers - "transfer link" between the control consoles and agent computers. Agents Are computers that directly attackserver by their requests. Both main computers and agent computers are, as a rule, "zombies", i.e. their owners do not know that they are participants in a DDoS attack.
The ways to protect against DDoS attacks are different depending on the type of attack itself. Among DDoS-attacks the following types are distinguished:
UDP flood - an attack by sending a lot of UDP packets to the "victim" address;
TCP flood - an attack by sending a lot of TCP packets to the "victim" address;
TCP SYN flood - an attack by sending a large number of requests to initialize TCP connections;
ICMP flood - an attack due to ICMP ping requests.
Attackers can combine these and other types of DDoS attacks, which makes such attacks even more dangerous and difficult to remove.
Unfortunately, universal methods of protection against DDoS-attacks does not exist. But compliance with some common rules will help reduce the risk of DDoS-attack, or as effectively as possible to combat its consequences.
So, to prevent a DDoS attack, you need toconstantly monitor the removal of vulnerabilities in the software used, increase resources and distribute them. Be sure to install at least a minimal package of protection programs from DDoS. This can be both conventional firewalls (firewalls) and special anti-DDoS programs. To detect DDoS-attacks should use special software and hardware systems.